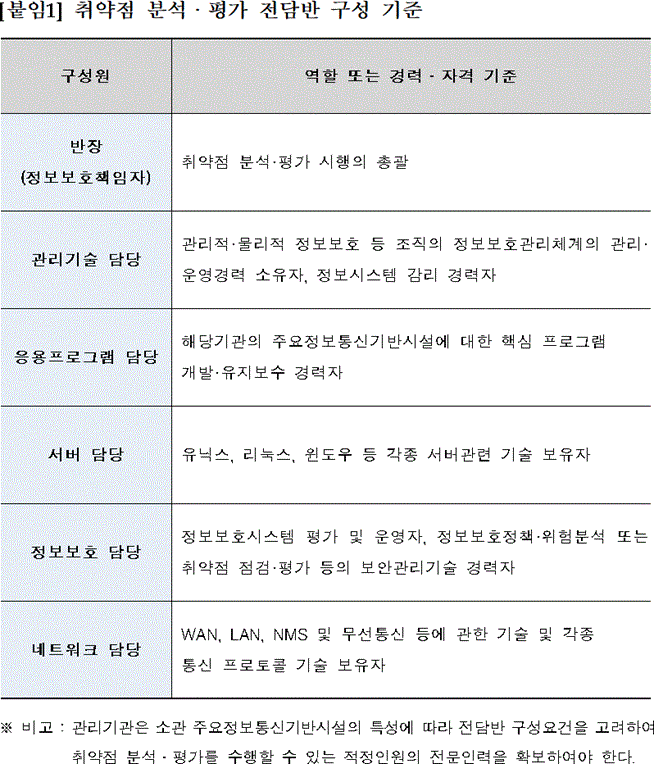
취약점 분석·평가 전담반 구성 기준
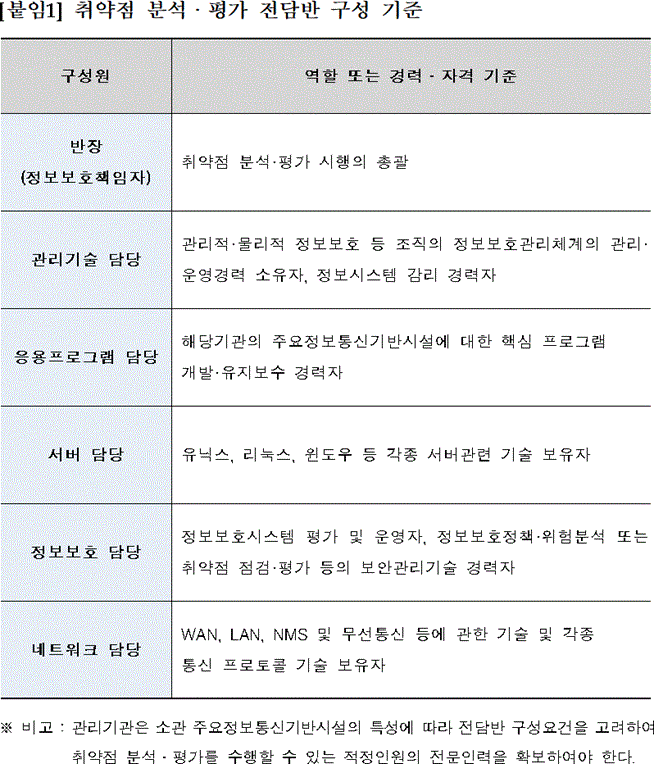
취약점 분석·평가 전담반 구성 기준
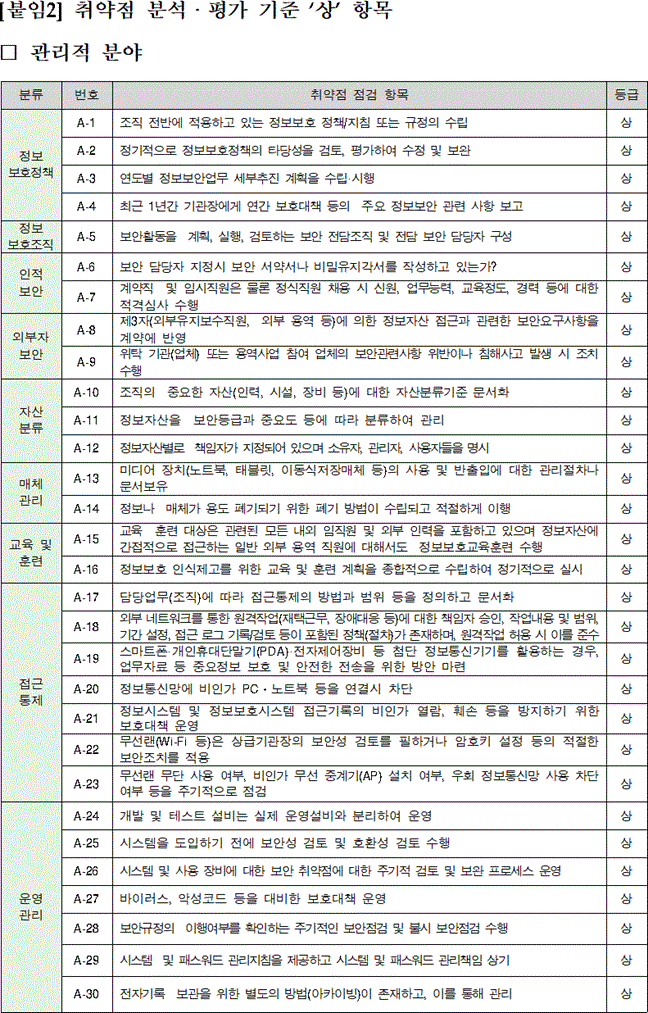
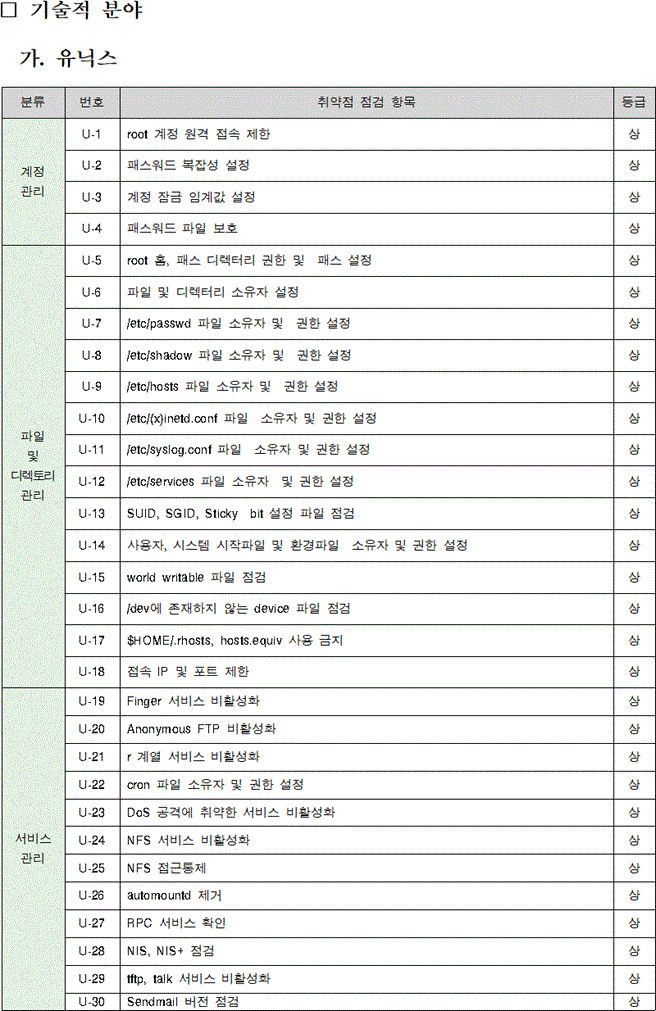
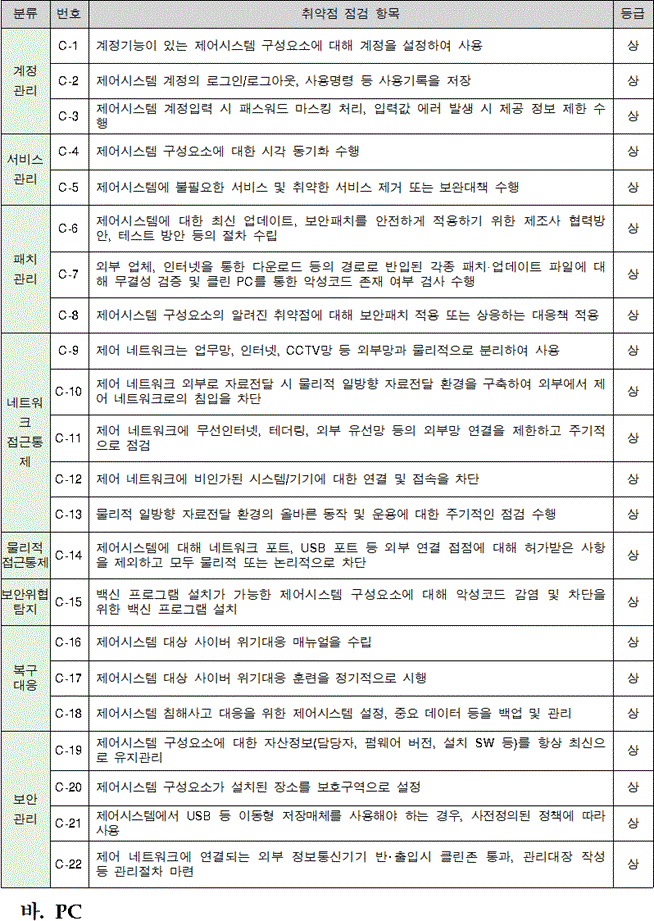
취약점 분석·평가 기준 '상' 항목-1
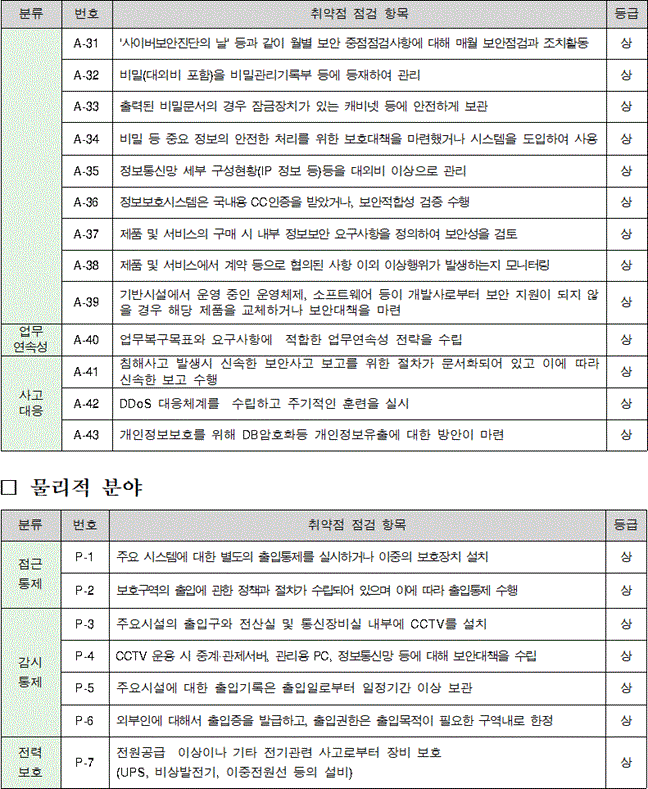
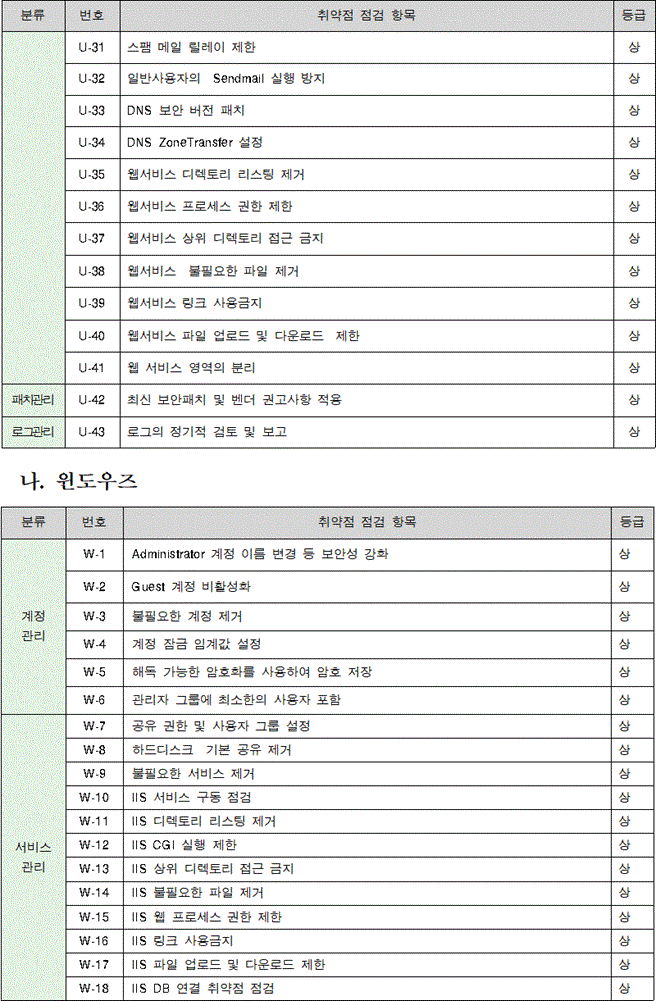
취약점 분석·평가 기준 '상' 항목-2
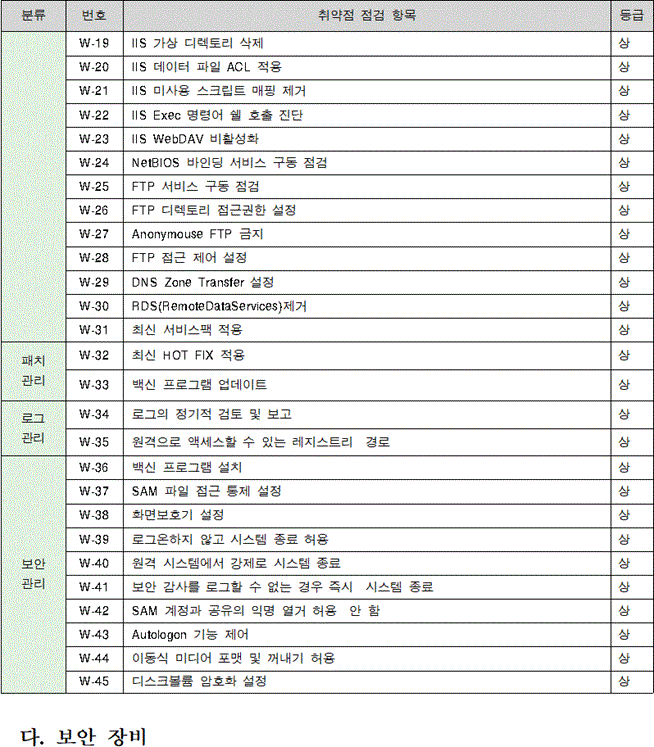
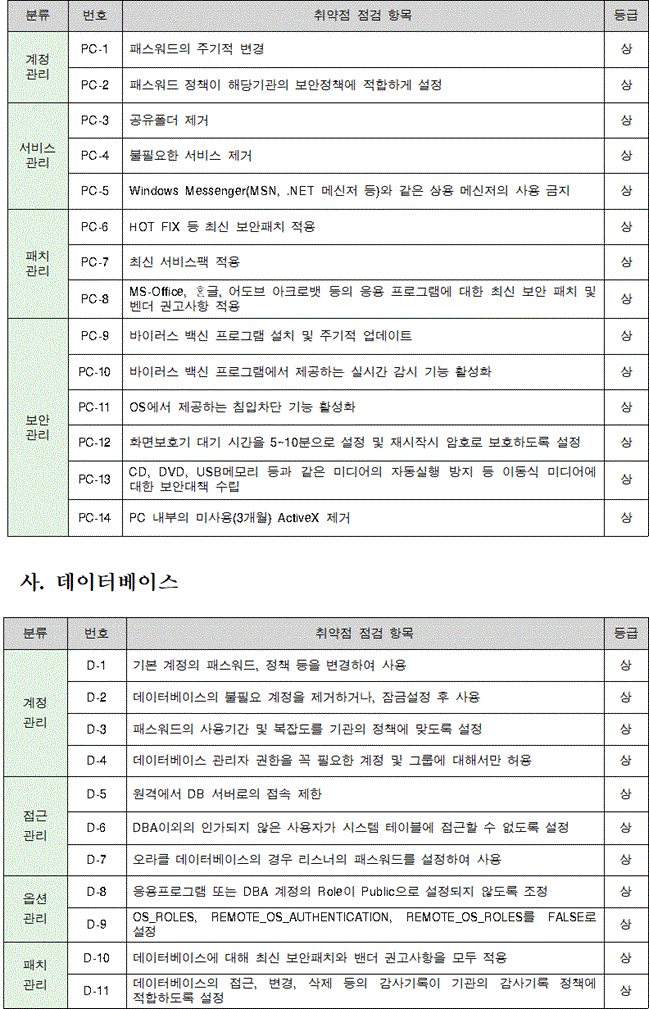
취약점 분석·평가 기준 '상' 항목-3
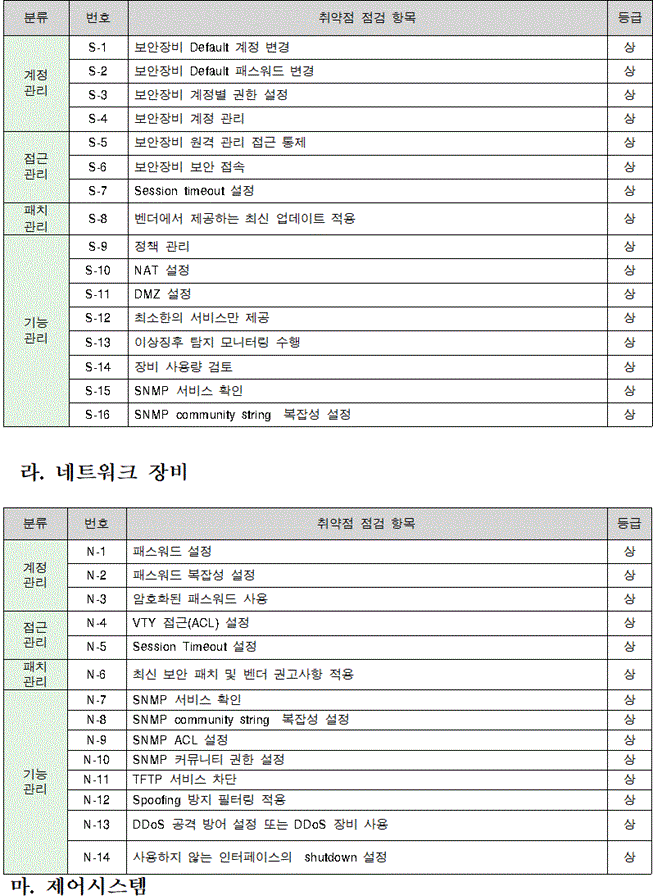
취약점 분석·평가 기준 '상' 항목-4
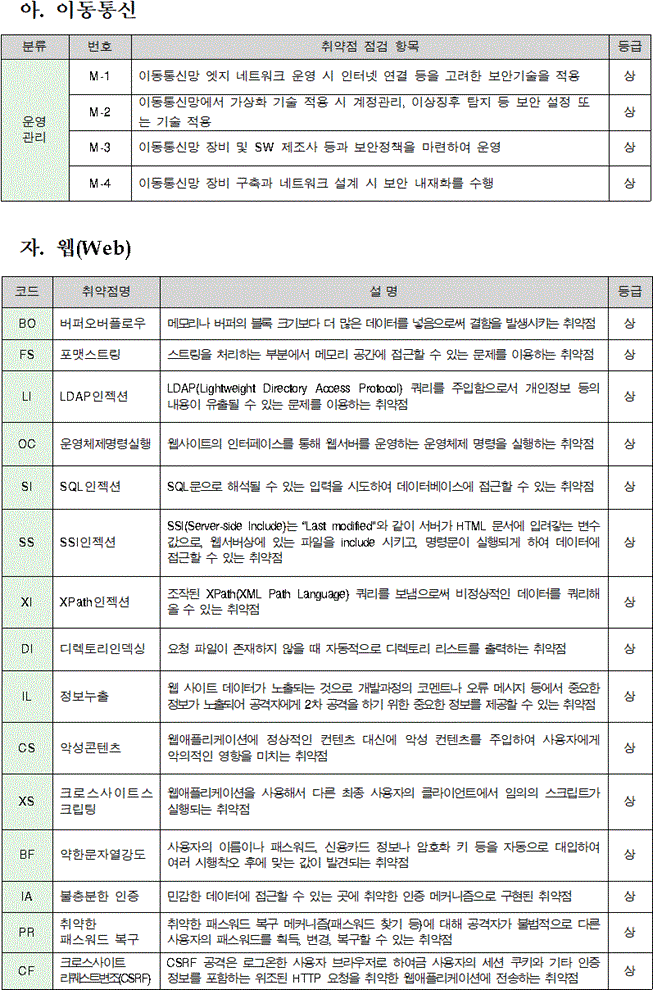
취약점 분석·평가 기준 '상' 항목-5
취약점 분석·평가 기준 '상' 항목-6
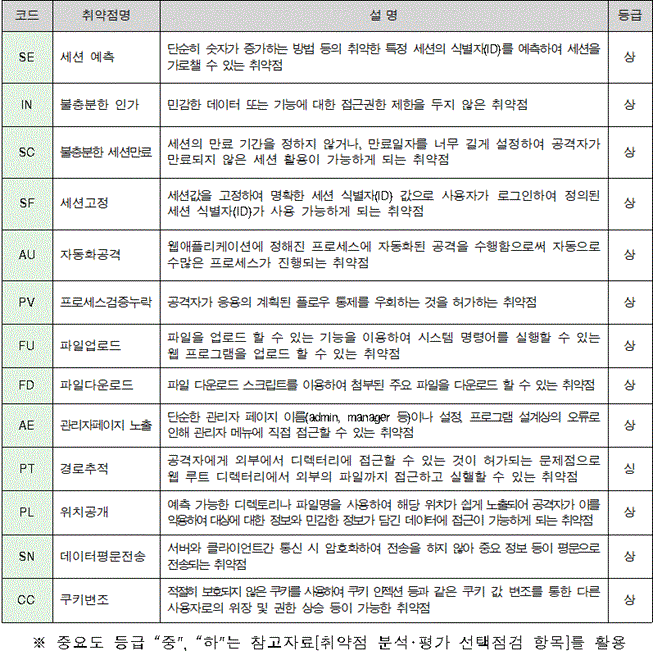
취약점 분석·평가 기준 '상' 항목-7
취약점 분석·평가 기준 '상' 항목-8
취약점 분석·평가 기준 '상' 항목-9
취약점 분석·평가 기준 '상' 항목-10
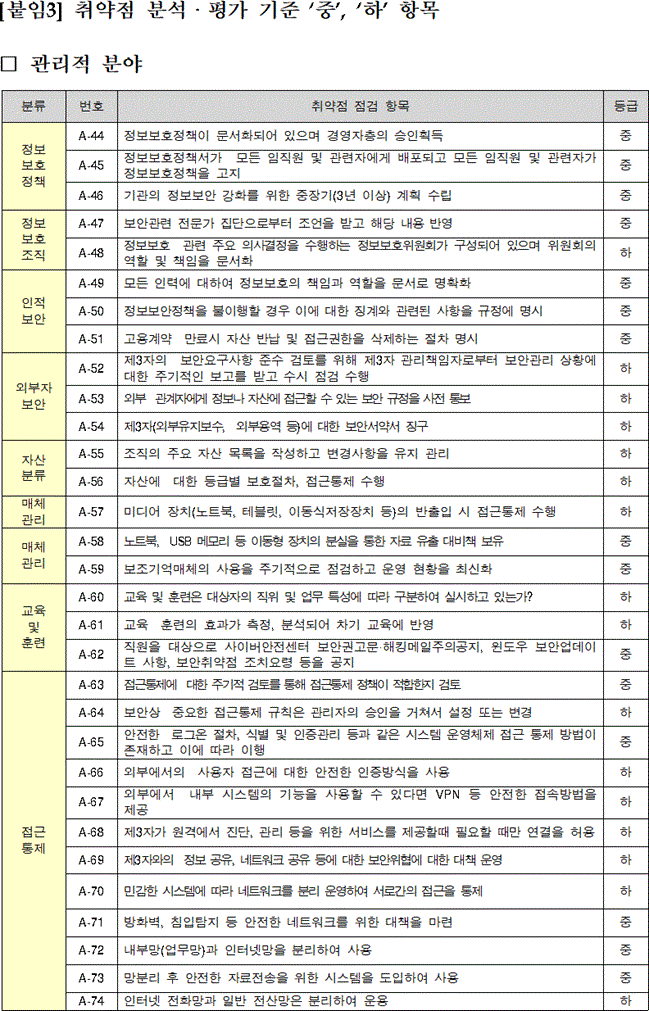
취약점 분석·평가 기준 '중', '하' 항목-1
취약점 분석·평가 기준 '중', '하' 항목-2
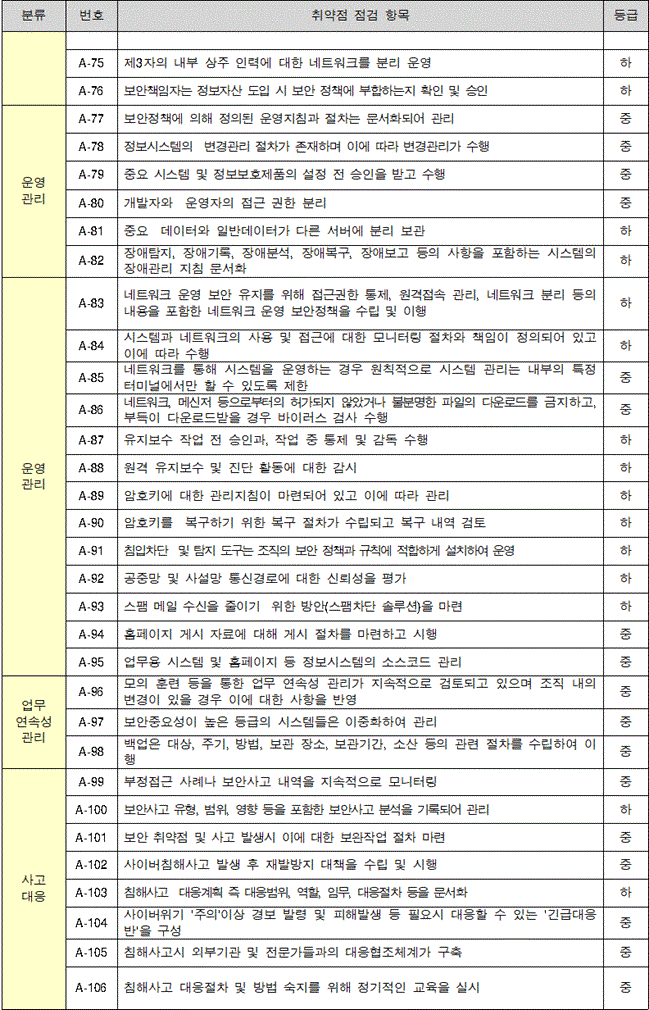
취약점 분석·평가 기준 '중', '하' 항목-3
취약점 분석·평가 기준 '중', '하' 항목-4
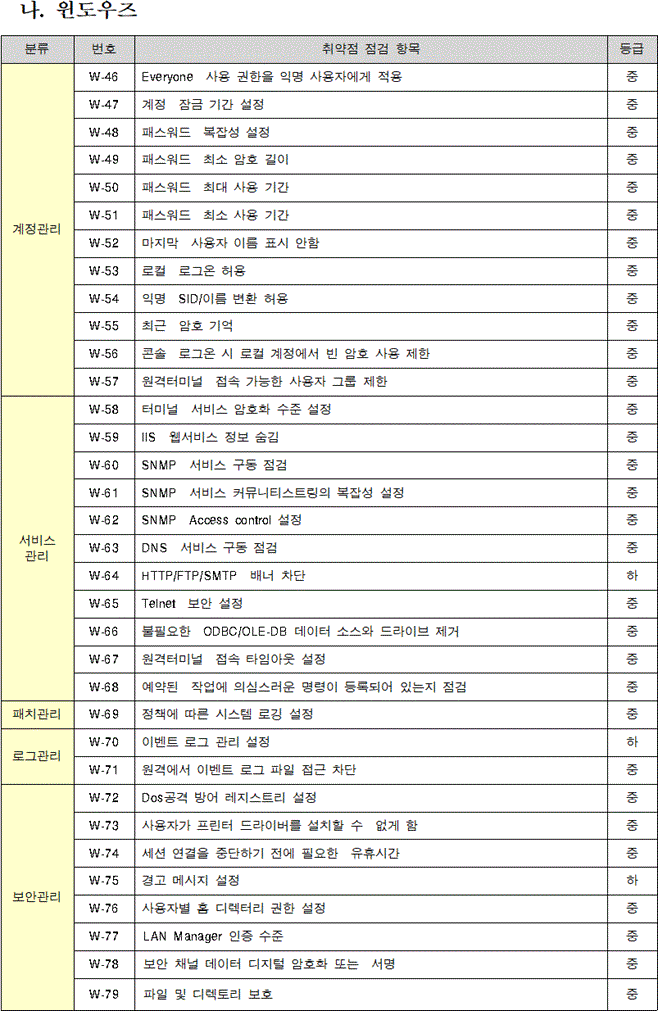
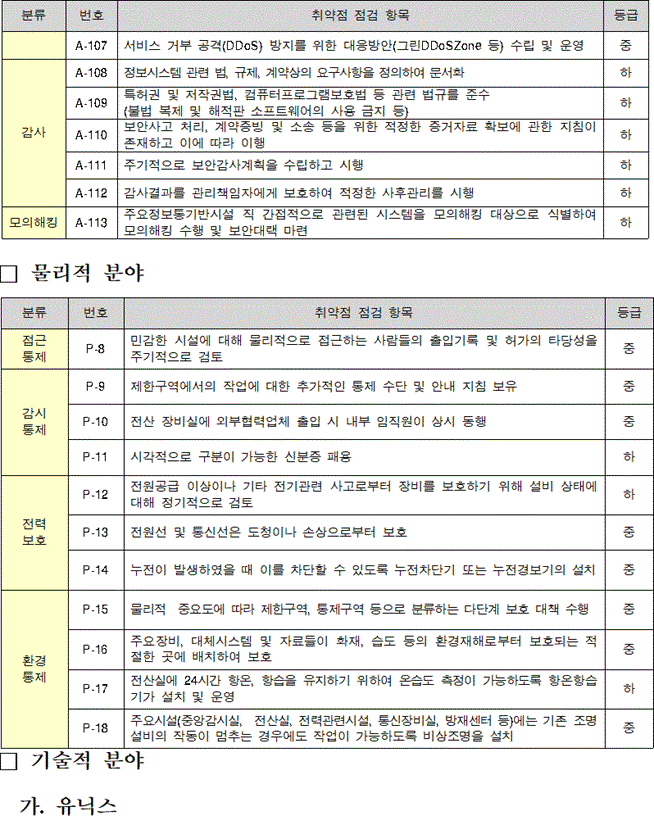
취약점 분석·평가 기준 '중', '하' 항목-5
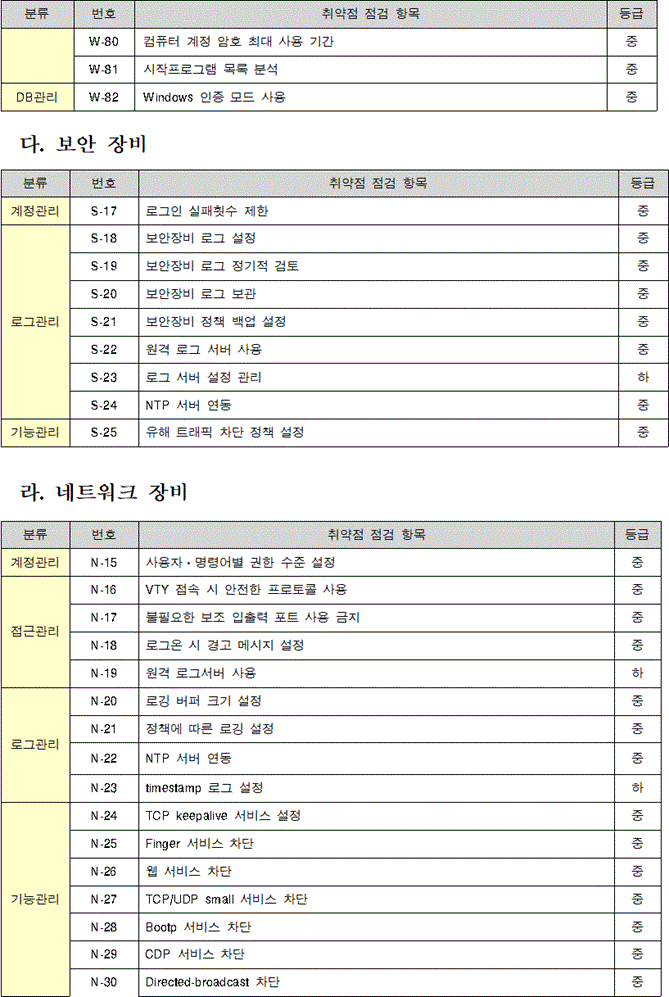
취약점 분석·평가 기준 '중', '하' 항목-6
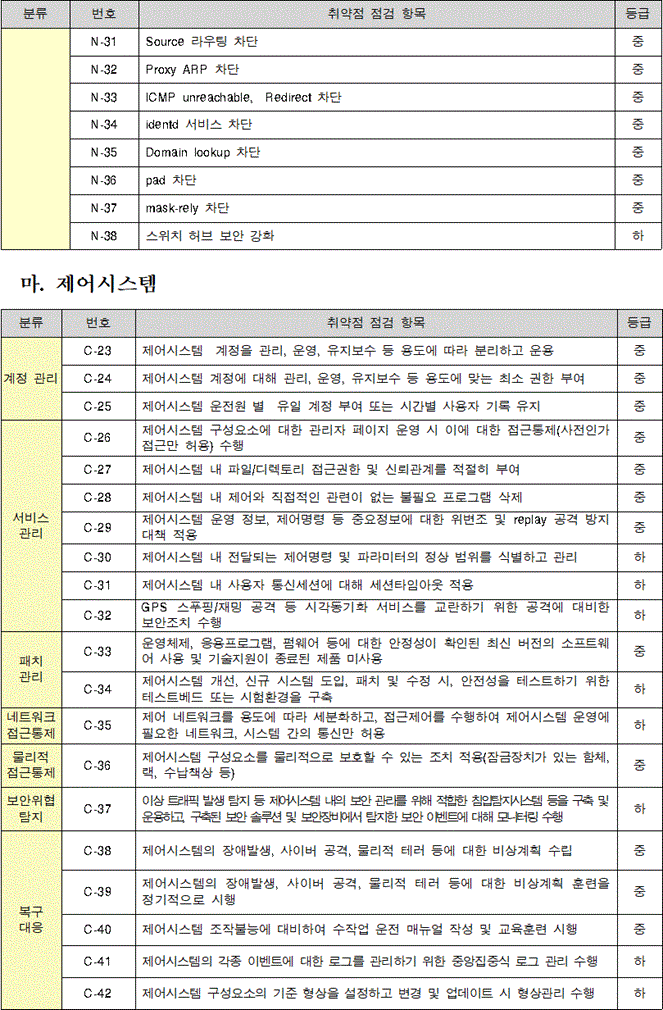
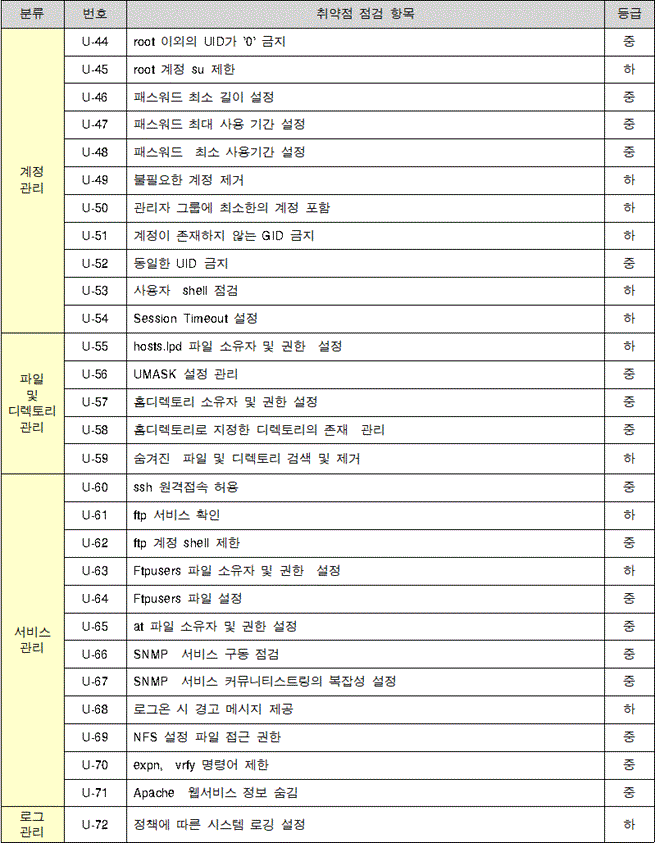
취약점 분석·평가 기준 '중', '하' 항목-7
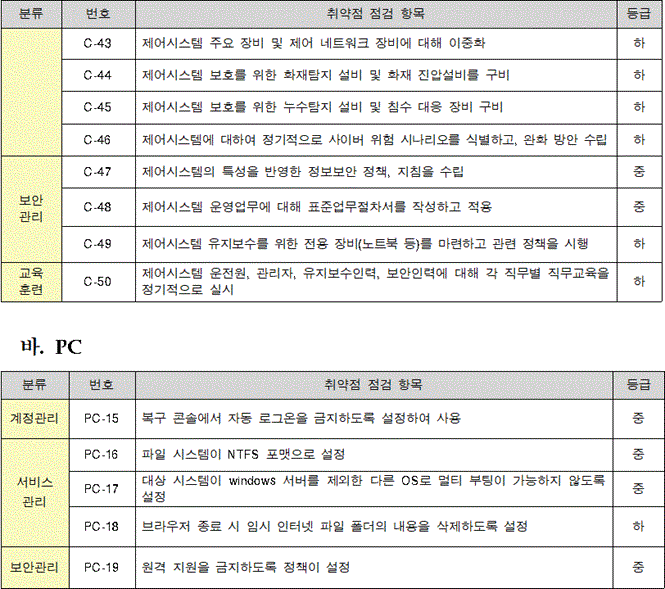
취약점 분석·평가 기준 '중', '하' 항목-8
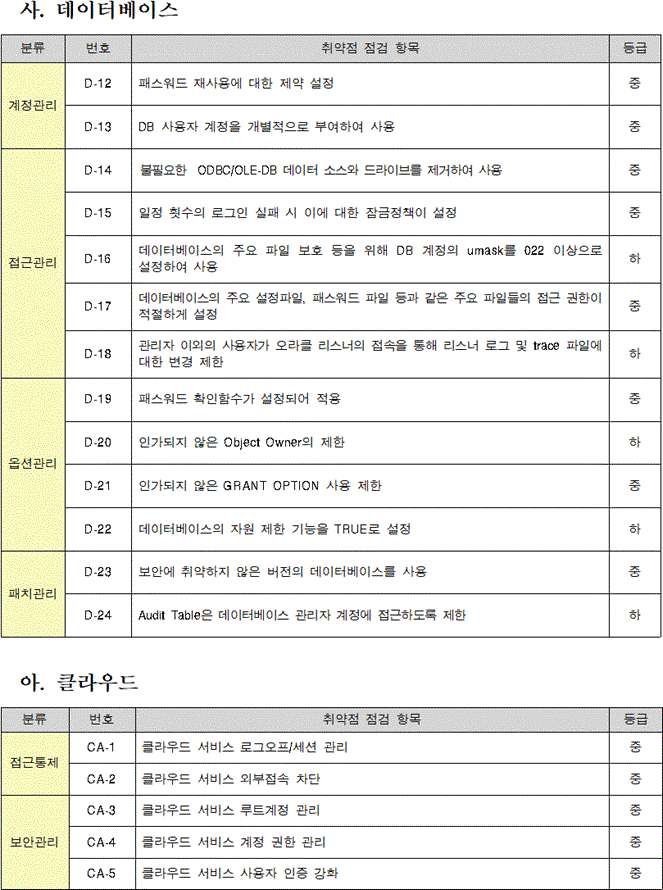
취약점 분석·평가 기준 '중', '하' 항목-9
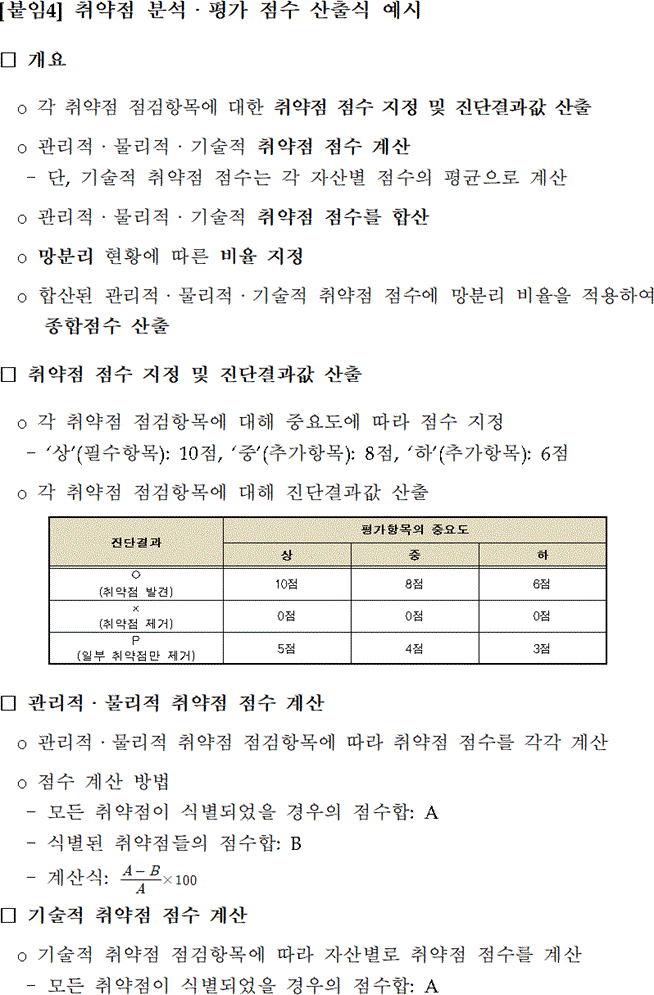
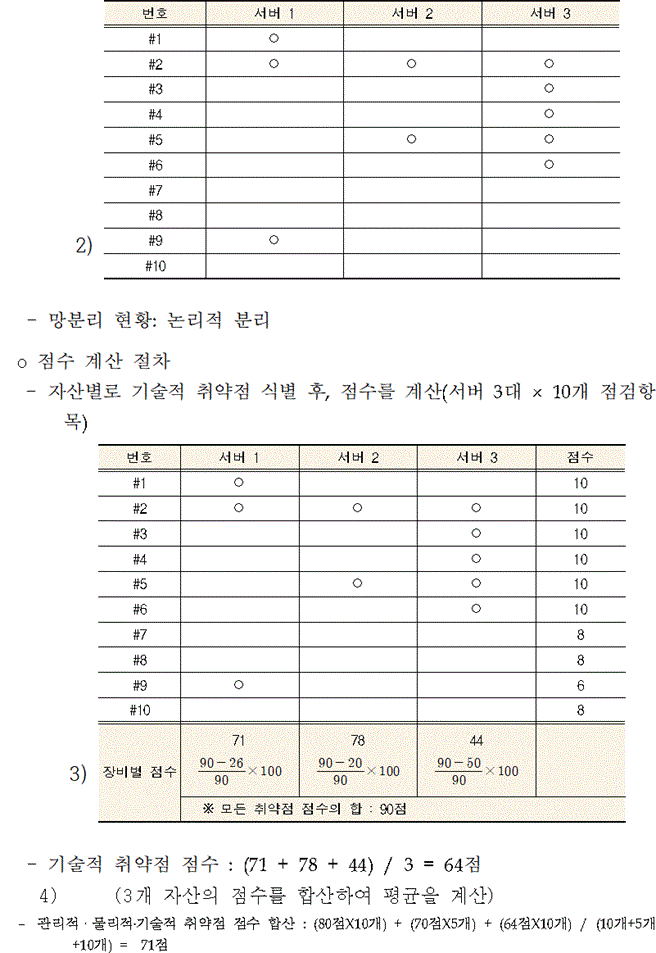
취약점 분석·평가 점수 산출식 예제-1
취약점 분석·평가 점수 산출식 예제-2
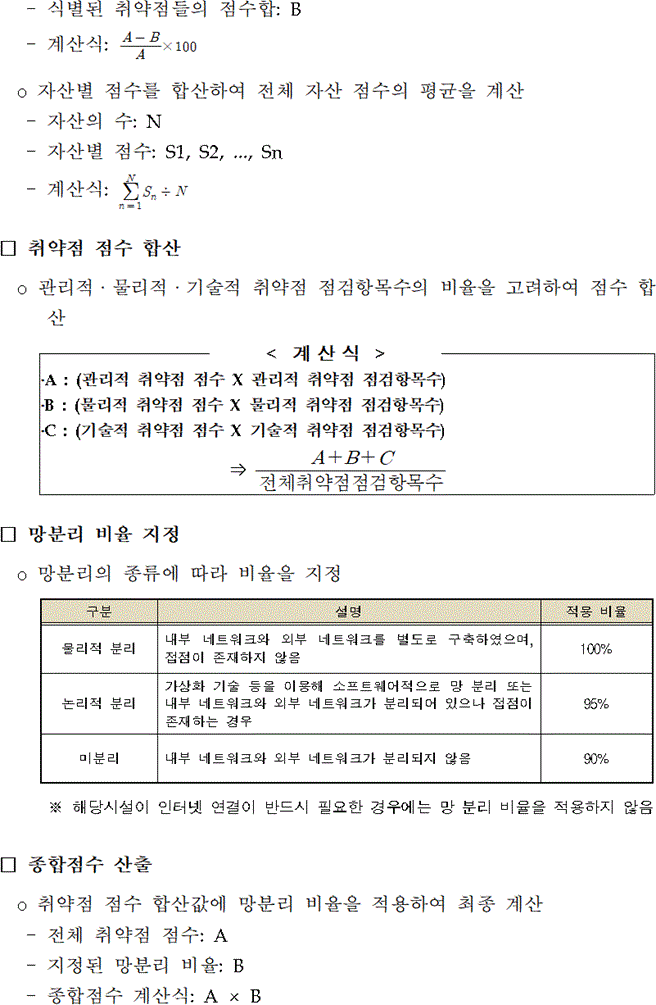
취약점 분석·평가 점수 산출식 예제-3
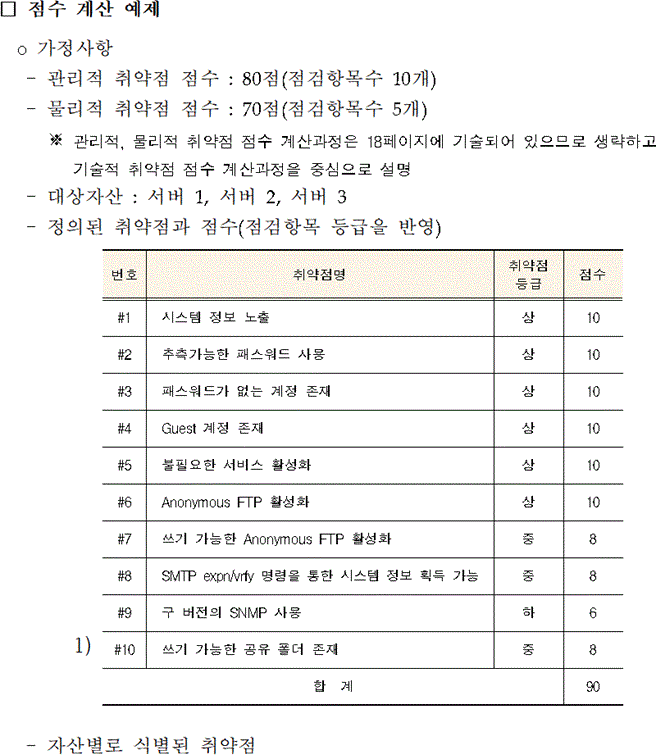
취약점 분석·평가 점수 산출식 예제-4
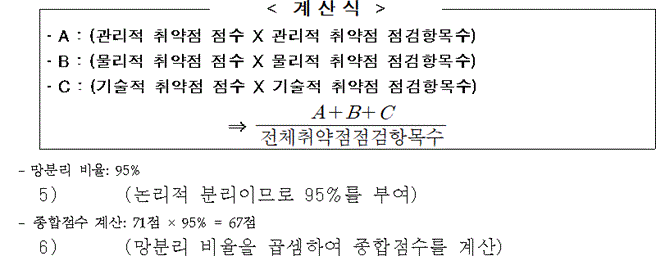
취약점 분석·평가 점수 산출식 예제-5